

By Nathan E. Malpass, Last updated: November 26, 2018
"Hello, I am hoping that you can help me. I recently bought myself a new Samsung mobile phone and in trying to keep my information secure, since I use my phone for work, I saved a new password, as well as a unique pin and pattern, and silly me forgot what those were.
Is there any way that I can get into my phone without using any of the usual ways?
I actually have a lot of work to do today on my phone and really need to access it as soon as possible. Is there any way that you can help me or do I need to bring my phone to my local service center and have the entire unit reset? Which I'm afraid might cause me to lose all the data I have thus stored in it…Hoping for your immediate assistance and crossing my fingers that you can give me good news! Thank you." - Single Mother in SFO
You may encounter the situation as what has been mentioned above. Now, let us see how to access a locked Android phone via USB.
Having concentrated on software development for some years, we have created an Android tool that is so powerful to meet people's needs.
Here is a tip for you: Download FoneDog Broken Android Data Extraction to easily and safely access your locked Android phone via USB and get your data. It is 100% safe and will help you extract your files without unlocking the phone. Free try it to get into your phone:
Broken Android Data Extraction
Recover photos, messages, WhatsApp, videos, contacts, call history from broken Samsung Phone.
Recover Data when you cannot enter the password on Android.
Complete Compatible with Samsung Galaxy devices.
Free Download
If you feel like doing it all on your own, we have gathered some common solutions to this situation below for you.
Part #1: IntroductionPart #2: What You Can Do To Retrieve The Data On Your Locked PhonePart #3: How To Backup Your Data Before Losing Everything On Your Android Mobile PhonePart #4: Tips and Tricks on How to Better Memorize Your Passwords without Making Them WeakPart #5: 4 Brilliant Methods To Creating A Secure PasswordPart #6: Conclusion
People Also ReadA Comprehensive Guide To Help Unlock Your Android PhoneCan You Unlock Phones for Free Using Codes? A Comprehensive Guide to Unlocking Your Phone
All mobile phones and devices have a screen lock function. They are there to secure your phone and to keep you from pressing buttons that you did not mean to press as well as to keep other people from entering your phone and deleting your precious photos, or worse, entering your bank details and transferring your money to their bank accounts!
Screen locks have come a long day since mobile phones were first released. In the early days of mobile phones, there was a simple two code combination that you had to press within 2 seconds in order to command the phone to unlock.
These days, we are able to personalize our screen locks through passcodes, pin numbers and/or letters, fingerprints, and even face recognition.
However, there have been cases when users have inputted a new PIN number but soon forgets what that PIN number of the combination was.
We try and try again only to realize that we are trying with old PIN numbers and cannot seem to remember what the right one was! You ask yourself, “why didn’t I write it down somewhere like I thought to do earlier?” You wonder, “what am I going to do about this problem?” You scream, “I need to get inside my phone! I’ve got work to do!!!”
Luckily for us all, there are options for us and the world is not over. There are ways to get into our phones in spite of not having the access to it via PIN number. This article is here to help you with that and we hope that you will find it helpful.
People Also Read:
How to Unlock Android Phone: Solutions & Tools
So your screen locks purpose is to keep out anyone who does not know your PIN code. But now that you yourself have forgotten your PIN code, what are your options?
Sadly, there is no straight up command or function, or series of moves that you can do with your phone that will unlock it. But, all is not lost. There are ways now that you can still enter your phone and recover photos, SMS messages, and other data even without your PIN code.
Enter, broken android data recovery. That’s right! You are not the first person who has had this problem and software developers have done their part in order to help you with this problem, just in case, on the off chance, it happens to you.
You see, these problems exist not only because you have forgotten your password or PIN code, but it has also happened to unfortunate users who have accidentally broken their screens thus making it impossible to type in their codes even if they haven’t forgotten it.
These android data recovery systems have become so advanced that they can now assist you in recovering photos, videos, contacts, SMS messages, music, files, and more! It is a massive step in technological advancements as this enables users to back up their data without losing anything, before having to go to the last option which would be a hard reset of your Android device and losing everything you have since obtained.
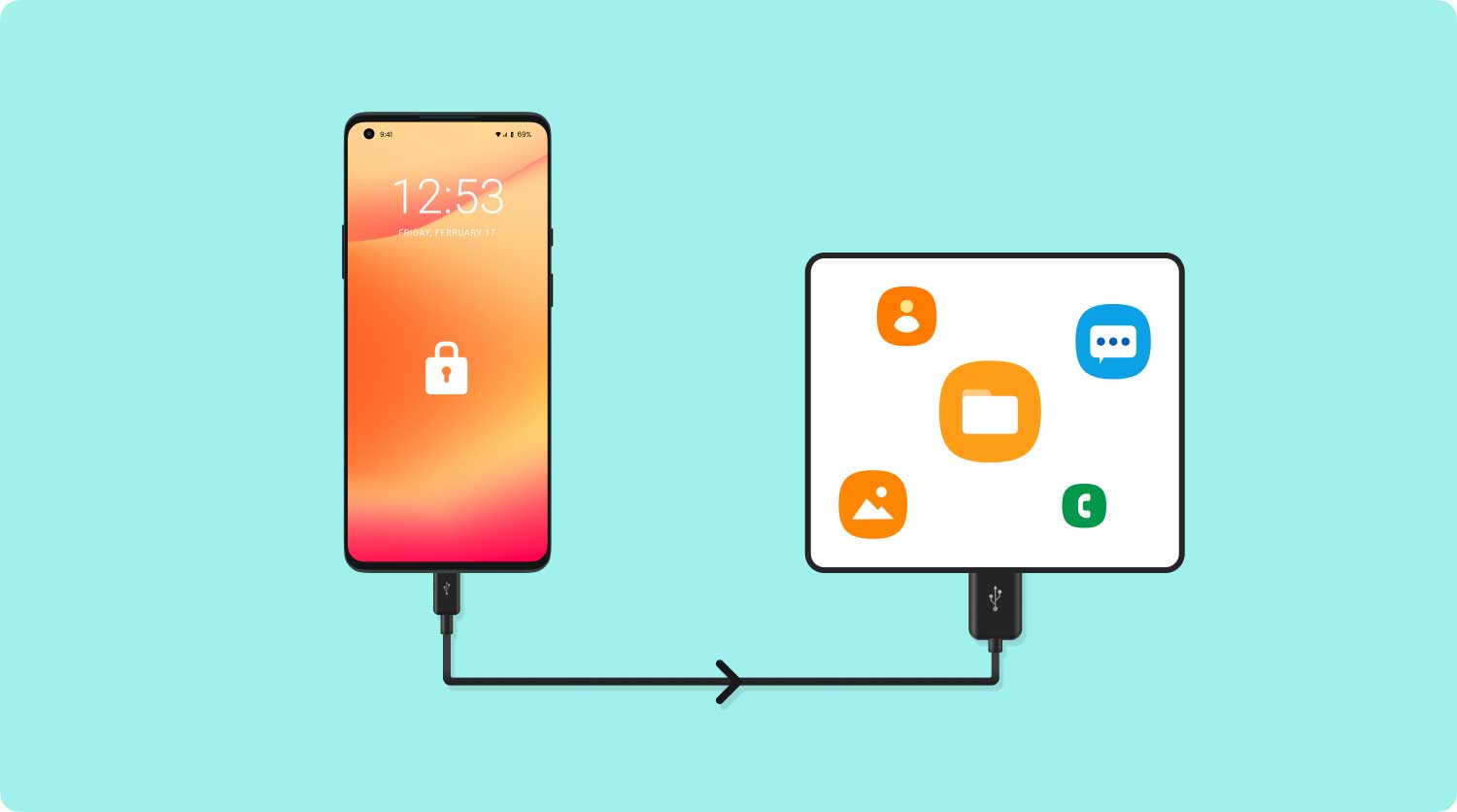
Luckily for us, there is a solution to backing up everything on your android phone without losing any of your data! There is a service that can provide you with the highest retrieval rate, it can recover everything from your photos to your messages to your videos to your WhatsApp and Viber, as well as your contacts and even your call history from your Android phone.
This solution can give you access to all of these, and more, when you are unable to access your android phone as a result of your device being locked, and is compatible with most Samsung Galaxy devices.
Not only will you be able to back up all your files but you can do so with the security that no one else will have access to these files and will enable you to transfer files through its preview function and offers you a 30 day free trial period in which you can test out its services while being assured that none of your data will be overwritten.
Broken Android Data Extraction
Recover photos, messages, WhatsApp, videos, contacts, call history from broken Samsung Phone.
Recover Data when you cannot enter the password on Android.
Complete Compatible with Samsung Galaxy devices.
Free Download
Considering that mobile phones are a major part of our world, both for personal and professional reasons, we must ensure that we never lose access to the data that we have collected.
We are aware that mobile phones tend to break and the screens of our android mobile phones are relatively fragile and can malfunction for a variety of reasons. They may crack, of the LCD may become thin causing it to cease existence.
So how does one recover this treasured data you ask? Below is a guide that will help you retrieve all your data without ever overwriting any of your previous content.
The first thing that you should do is to download the FoneDog Toolkit for Android. It can be found in your Play Store and we can help you back up your data through a step by step tutorial.
Download and launch the FoneDog Toolkit onto your android phone. Make sure you connect your android mobile phone to your computer and begin by clicking on the “Broken Android Data Extraction” button.
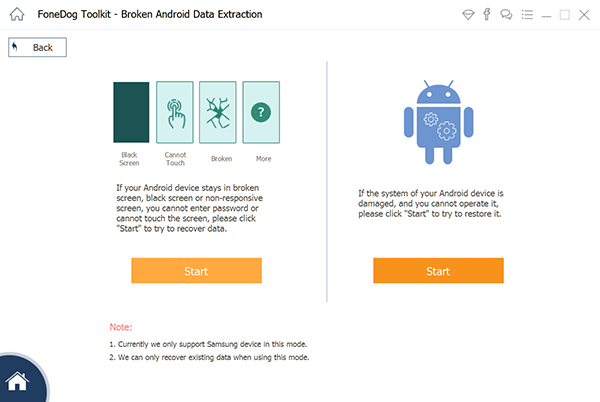
Select the type that matches the situation you are dealing with. At this point, the FoneDog Toolkit - Broken Android Data Extraction system will ask you the exact problem that you are experiencing on your broken android mobile phone.
This may be one of the following: “Touchscreen doesn’t work”, “Cannot access the phone”, or “Black/broken screen”. In the case of being locked out of your Android device, click on the “Black/broken screen” option.
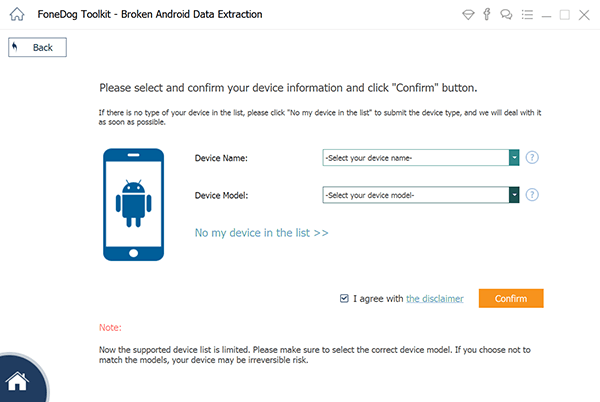
Choose your device and model of your android mobile phone. The FoneDog Toolkit - Broken Android Data Extraction software will now ask you to program in the exact name and model of the android phone you are using before you will be allowed to proceed with your task.
By doing this, you are in effect giving permission to the software the right to download the correct system it needs in order to access and extract data from your Android phone into your computer.
Once you have entered the requested name and model of your android mobile phone, you can simply click “next” in order to proceed towards the next steps that you need to follow.
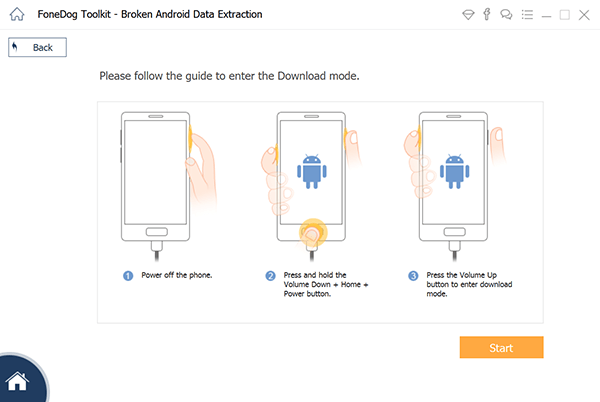
Enter into the realm of your download mode. For this, you will need to do the following tasks in order to begin. Start by powering off your android mobile phone.
Then press and hold the volume - button, while holding the Home and Power button at the same time. After that, press the volume + button and now you will be able to enter the download mode.
Download your recovery package. Once you have successfully set your phone to download mode, the FoneDog Toolkit - Broken Android Data Extraction application will begin analyzing the contents of your phone or android tablet and will begin to download the recovery package.
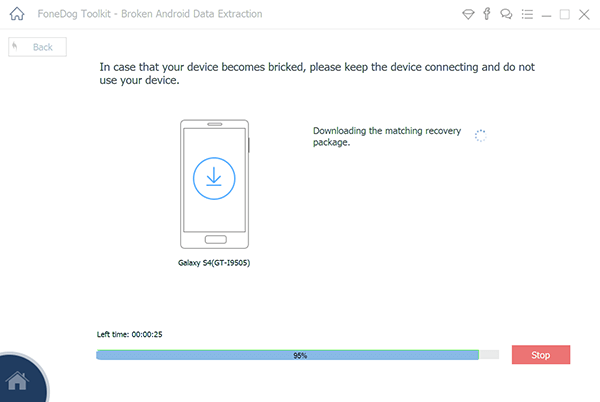
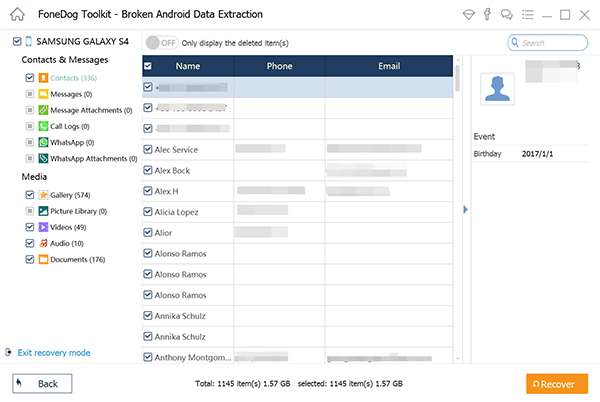
Begin scanning, previewing, and recovering data from your locked android mobile phone. After the completion of the system’s scanning, previewing, and extracting your mobile phone’s data, you will now be shown the different categories of the files that the system has been able to recover.
At this point, you may begin choosing which important data is stored in the internal memory of your locked android phone. On the left side of your screen, you will see all the categories on the left window of your screen.
Click on “recover” at the bottom of your screen and the files will automatically be saved onto your computer where it will be a breeze for you to copy those files back into a new android mobile phone.
Note in the end:
Please make sure whether your Android device model is supported by FoneDog Broken Android Data Extraction: https://www.fonedog.com/broken-android-data-extraction/reference.html.
We live in a world where we have tons of passwords. It seems as if we have a password for everything that we do. We may sometimes have only one email address but we can link that email address to tens of accounts, all of which are capable of carrying their own password.
As a result, we tend to forget our passwords sometimes even within minutes of creating a profile on any one of a thousand websites.
It may even be that we use the same password over dozens of websites and needless to say, that is not really the smartest thing you can do if you want to keep your profiles secure from other people.
It is for this reason that we have come up with a list to help you memorize these precious passwords. These tips are meant to help you keep your passwords unique while retaining the memory in order to never have trouble figuring out what your passwords are. We hope that these work for you too.
Security masters McAfee suggests creating a tip sheet which contains clues to your passwords while not needing to list down what those actual passwords are to anyone who could be looking over your shoulder as you view these tips.
But one must keep in mind that writing cryptic clues is only helpful if these are unique only to you. If these tips are obvious to other people other than yourself, then this somewhat defeats its purpose.
What some masters practice is writing the first letter of their password followed by a clue as to what that password is. Others use rhyme or numbering, while some may even use book titles or songs. What must matter is that the clue jogs your memory and helps you figure out what the actual password is.
As an added tip to writing down your password, do not keep it next to your computer. There are many good hiding spots around where you are, so choose your spot wisely.
Sometimes people use the name of a website or the shape of its logo as a tool to help them create a memorable yet secure password.
For example, if creating a password for Facebook, you could create a password using F or even FB as the opening letting to your password. One other option that you might want to experiment with is using a trigger.
The example here could be using F for favorite food, and the actual password could somehow be connected to that dish or meal or even restaurant.
This is relatively common and highly effective. What it is is merely replacing a few letters with numbers of spelling words wrong on purpose.
You can also try abbreviations in order to come up with a solid password while retaining how easy it can be to memorize. One example would be using the word “password” by writing it down as P@ssW0rd.
Not only are you securing your profile but now you are also allowed to spell words wrong without anyone grading or judging you.

You could choose any number of words but we would say that four should suffice. Think of a line in a movie, or a song lyric, or a poem, or a series of words in a book that are very close to you and that you would never forget.
Once you have thought of something that you are sure you will always remember, select four words within that line and put them together. Your results could be spectacular and you will never forget that password.
For example, if I want to use the title of the book “Where The Wild Things Are”. I could create my password as Wh3r3Th3Wild@re which is code for Where The Wild Are.
I would say that this is a pretty secure password and not something that a hacker, or anyone else for that matter, could easily break through.
A security expert Named Bruce Schneier announced the method in 2008 and swears by it until today. It is similar to Tip #5 in Part 4 but works like a charm every single time.
What you do is you take a sentence, any sentence at all, and the turn it into a password. You simply remove some words from the sentence and abbreviate or combine any number of ways to create your secure password.
The Electrum Method of creating a password was done so from protecting passwords used for Bitcoins. Needless to say, these passwords protect very high levels of security and rely on safe passwords with utmost importance.
The Electrum Method is also known as the passphrase, which represents a relatively new way of thinking of your security and recommends using a 12-word seed.
Not sure how to begin? Think of 12 words that compose a sentence you will never forget. From there simply grab 4 of its words and then you’re done. You’ve created a 4-word password that would be doubtful for anyone to crack.
Here is an example with 13 words, the chorus of the popular Doors song “Light My Fire.” It does, “come on baby light my fire, try to set the night on fire.” Your password could be any one of 4 words here such as “comelightnightfire” or “babytrytofire”.
The PAO Method is otherwise known as the Person-Action-Objective method and is said to create passwords that are unbreakable. To use this method, think of an interesting place such as the Statue of Liberty.
Then think of a famous person, for the sake of this article, we will use Tom Cruise. Finally, imagine a random action such as driving a car. For this, you have technically created the phrase “Tom Cruise drives a car to the Statue of Liberty.”
With the PAO Method of memorization, your cognitive skills kick in while your brain memorizes the visuals that are created from the scenario you just created. At this point, you may now create your password using any number of words from that scenario you had come up with.
Here’s a quick example of how one might do this. First, log on to the internet and go to any random password memory generator website. Come up with 20 different passwords that have a minimum of 10 characters each.
Feel free to use punctuations and capital letters as you go along. From here, scan the passwords while attempting to locate phonetic structures. You may want to start by using that sort of ring in your head first.
Once done, type out your phonetic passwords in a text file noting that the easier to type the password, the easier it is to get stuck in your head.
Broken Android Data Extraction
Recover photos, messages, WhatsApp, videos, contacts, call history from broken Samsung Phone.
Recover Data when you cannot enter the password on Android.
Complete Compatible with Samsung Galaxy devices.
Free Download
We are all very lucky. In spite of our addiction and need to remain glued to our Android devices, and the fact that they can be faulty and cause us problems, we still are able to manage to continue using these devices practically without any signs of problems.
If it weren’t for great Android mobile phone manufacturers and application software developers, where would we be?
But remember, do yourself a favor as well and take care of what is yours. Though we have ways around problems like being able to back up your information, it is always best to use your phone in its simplest form in order to lengthen its lifespan and by doing so, it too will treat you right.
Leave a Comment
Comment

Laura Daniela2019-06-26 16:21:28
Buenos Dias, hace algunos días deje caer mi celular (Samsung J5) y al recogerlo y encenderlo aparentemente no le había ocurrido nada, al correr algunos minutos apareció un ligero tinte rosado en una esquina inferior al correr el tiempo esta se iba volviendo mas grande y de tonalidad mas oscura, cada vez la pantalla de mi celular se iba volviendo negra poco a poco, hasta que alcanzo la totalidad de la pantalla y ya no lo podía usar. Me gustaría saber si hay alguna manera de acceder al celular y a todas sus aplicaciones desde un pc o algún otro dispositivo , ya que realmente y de manera urgente necesito acceder a algunas de esas aplicaciones a las que ya no puedo tener acceso. Muchas Gracias!
Android Toolkit
Recover deleted files from your Android phone and tablet.
Free Download Free DownloadHot Articles
/
INTERESTINGDULL
/
SIMPLEDIFFICULT
Thank you! Here' re your choices:
Excellent
Rating: 4.6 / 5 (based on 80 ratings)